Online Training Course
ISC2 CISSP
N2K’s CISSP Training Course enables practitioners to participate, learn, and partner with other professionals as they prepare to earn the highly in-demand CISSP certification.

Who should earn the CISSP
The CISSP is an advanced certification designed for experienced practitioners, managers, and executives. It covers a wide range of cybersecurity topics across eight domains. This credential is well-suited for those in or aspiring to the following positions:
The CISSP is an elite way to demonstrate your knowledge, advance your career and become a member of a community of cybersecurity leaders. It shows you have all it takes to design, engineer, implement and run an information security program. The CISSP also meets the U.S. Department of Defense Directive 8570/8140.
Chief Information Security Officer
Director of Security
IT Director/Manager
Security Systems Engineer
Security Analyst
Security Manager
Security Auditor
Security Architect
Security Consultant
Network Architect
Course Overview
As ISC2 Official Training Provider, N2K’s CISSP Training Course enables practitioners to participate, learn, and partner with other professionals as they prepare to earn the CISSP certification.
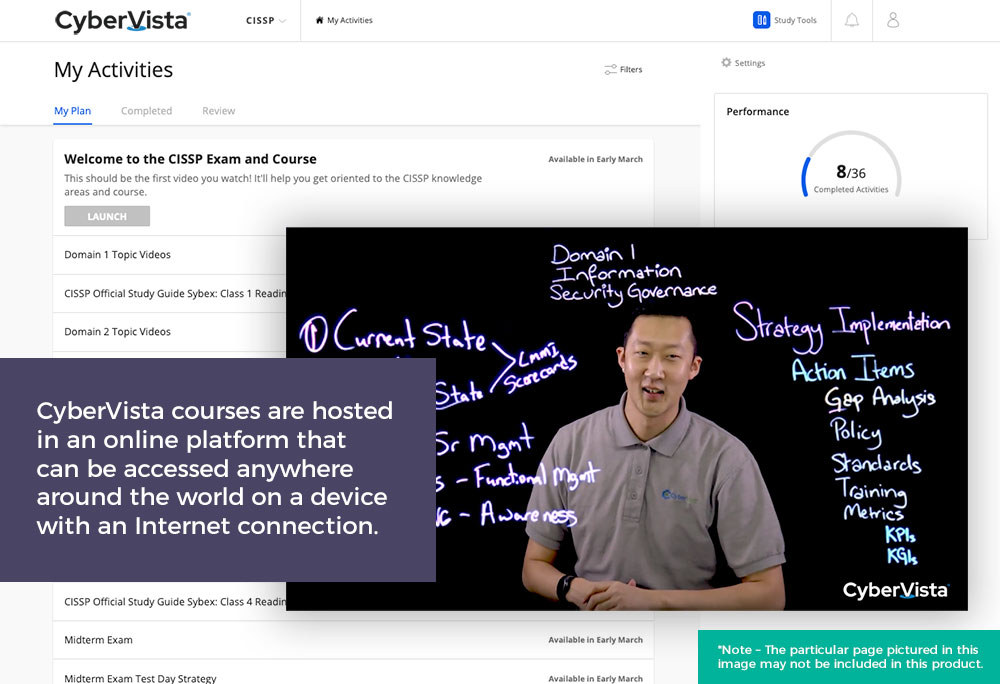
We offer CISSP as a Video On-Demand Course that allows participating practitioners to move at their own pace.
Readiness guarantee – CyberVista offers a course readiness or retake guarantee on all Certify courses. If any individual taking this training course does not pass the exam on the first try or does not feel prepared following the completion of the course can retake the course at no additional charge for up to one full year.
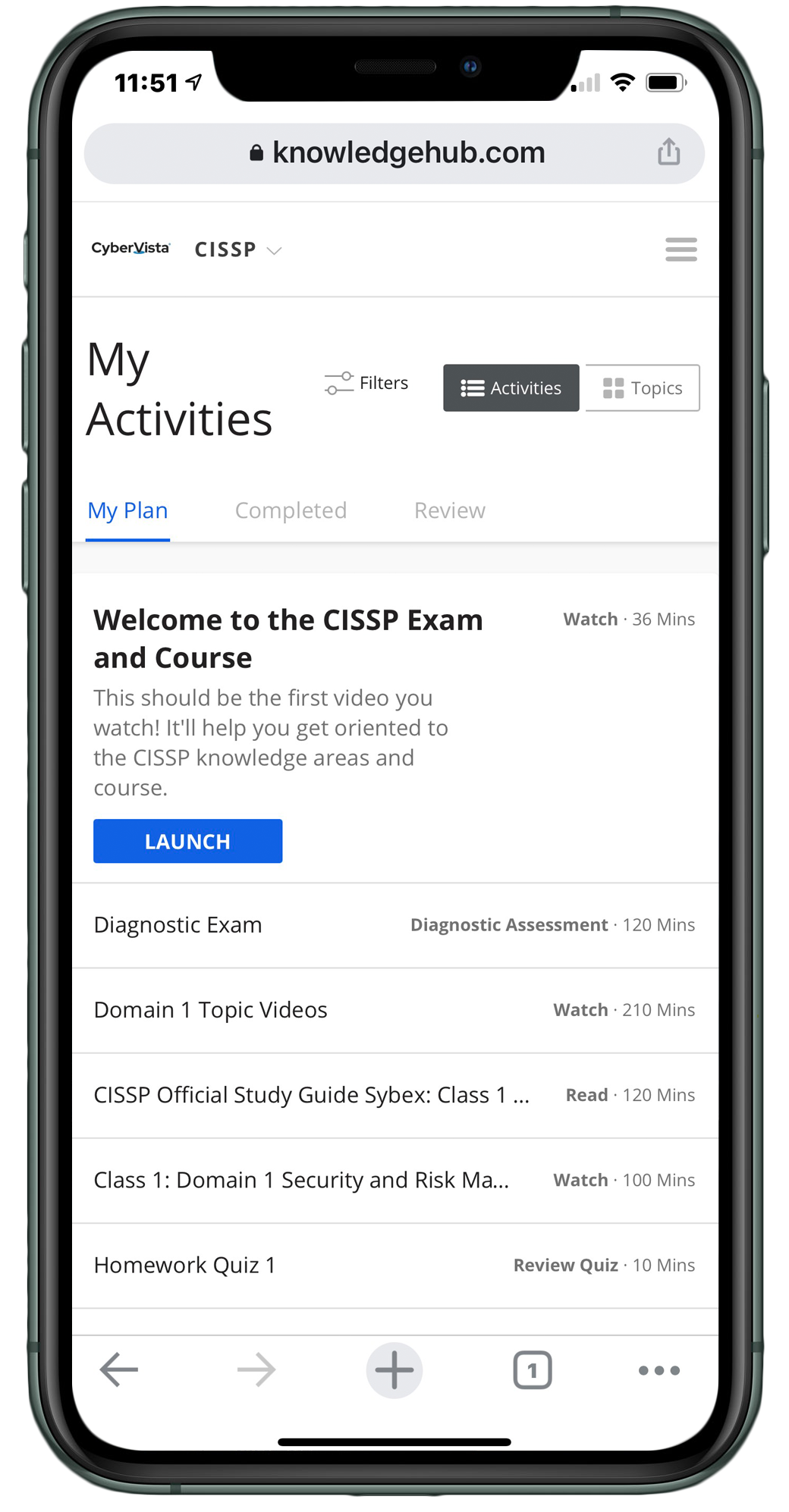
This course includes:
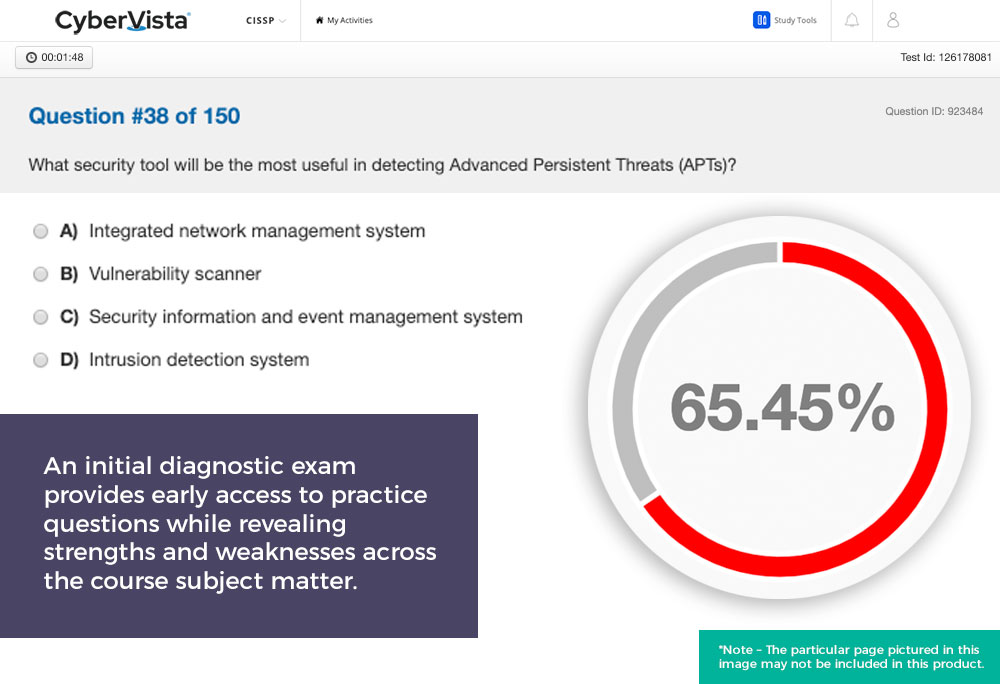
- 100 question diagnostic exam
- CAT (Computer Adaptive Test) final exam
- 700+ digital flashcards
- 100 question mid-term practice exam
- 140+ 5-15 minute on-demand training videos
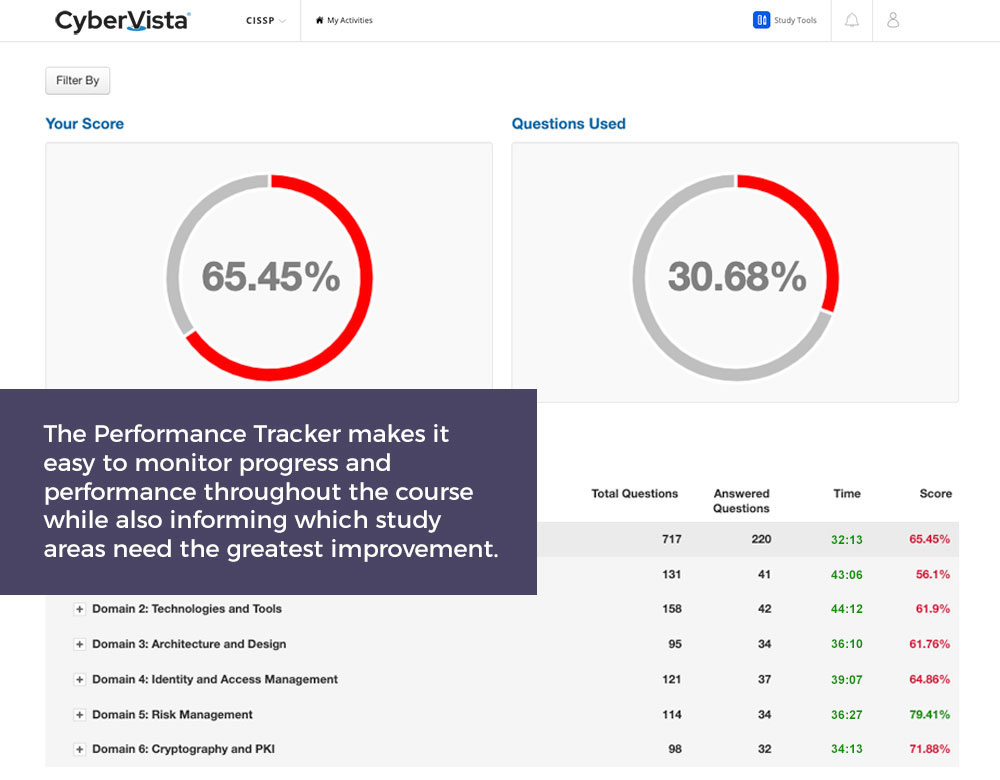
- Performance Tracker
- 1:1 private study session
- 800+ practice question bank
- Summary Notes
- Summary Videos
- Official (ISC)² Guide to the CISSP (9th ed.)
- The CISSP CBK Student Handbook (e-book)
Course Outline
Domain 1: Security and Risk Management
- 1.1 Understand, adhere to, and promote professional ethics
- 1.2 Understand and apply security concepts
- 1.3 Evaluate and apply security governance principles
- 1.4 Determine compliance and other requirements
- 1.5 Understand legal and regulatory issues that pertain to information security in a holistic context
- 1.6 Understand requirements for investigation types (i.e., administrative, criminal, civil, regulatory, industry standards)
- 1.7 Develop, document, and implement security policy, standards, procedures, and guidelines
- 1.8 Identify, analyze, and prioritize Business Continuity (BC) requirements
- 1.9 Contribute to and enforce personnel security policies and procedures
- 1.10 Understand and apply risk management concepts
- 1.11 Understand and apply threat modeling concepts and methodologies
- 1.12 Apply Supply Chain Risk Management (SCRM) concepts
- 1.13 Establish and maintain a security awareness, education, and training program
Domain 2: Asset Security
- 2.1 Identify and classify information and assets
- 2.2 Establish information and asset handling requirements
- 2.3 Provision resources securely
- 2.4 Manage data lifecycle
- 2.5 Ensure appropriate asset retention (e.g., End-of-Life (EOL), End-of-Support (EOS))
- 2.6 Determine data security controls and compliance requirements
Domain 3: Security Architecture & Engineering
- 3.1 Research, implement and manage engineering processes using secure design principles
- 3.2 Understand the fundamental concepts of security models (e.g., Biba, Star Model, Bell-LaPadula)
- 3.3 Select controls based upon systems security requirements
- 3.4 Understand security capabilities of Information Systems (IS) (e.g., memory protection, Trusted Platform Module (TPM), encryption/decryption)
- 3.5 Assess and mitigate the vulnerabilities of security architectures, designs, and solution elements
- 3.6 Select and determine cryptographic solutions
- 3.7 Understand methods of cryptanalytic attacks
- 3.8 Apply security principles to site and facility design
- 3.9 Design site and facility security controls
Domain 4: Communication & Network Security
- 4.1 Assess and implement secure design principles in network architectures
- 4.2 Secure network components
- 4.3 Implement secure communication channels according to design
Domain 5: Identity & Access Management (IAM)
- 5.1 Control physical and logical access to assets
- 5.2 Manage identification and authentication of people, devices, and services
- 5.3 Federated identity with a third-party service
- 5.4 Implement and manage authorization mechanisms
- 5.5 Manage the identity and access provisioning lifecycle
- 5.6 Implement authentication systems
Domain 6: Security Assessment & Testing
- 6.1 Design and validate assessment, test, and audit strategies
- 6.2 Conduct security control testing
- 6.3 Collect security process data (e.g., technical and administrative)
- 6.4 Analyze test output and generate report
- 6.5 Conduct or facilitate security audits
Domain 7: Security Operations
- 7.1 Understand and comply with investigations
- 7.2 Conduct logging and monitoring activities
- 7.3 Perform Configuration Management (CM) (e.g., provisioning, baselining, automation)
- 7.4 Apply foundational security operations concepts
- 7.5 Apply resource protection
- 7.6 Conduct incident management
- 7.7 Operate and maintain detective and preventive measures
- 7.8 Implement and support patch and vulnerability management
- 7.9 Understand and participate in change management processes
- 7.10 Implement recovery strategies
- 7.11 Implement Disaster Recovery (DR) processes
- 7.12 Test Disaster Recovery Plans (DRP)
- 7.13 Participate in Business Continuity (BC) planning and exercises
- 7.14 Implement and manage physical security
- 7.15 Address personnel safety and security concerns
Domain 8: Software Development Security
- 8.1 Understand and integrate security in the Software Development Life Cycle (SDLC)
- 8.2 Identify and apply security controls in development environments
- 8.3 Assess the effectiveness of software security
- 8.4 Assess security impact of acquired software
- 8.5 Define and apply secure coding guidelines and standards
"I would not have passed the CISSP exam without Cybervista! The instructors were knowledgeable and helpful in grasping the material... The weekly online lessons were extremely helpful in breaking down each of the domains covered on the exam. If you follow the study plan provided and put in the time required to understand the major concepts outlined by CyberVista, you’ll pass!"
"When I was training I found myself using CyberVista’s quiz bank a lot, plus they tested me in other ways such as the initial diagnostic exam, the midterm, and the final exam. Getting used to the wording and doing all those practice questions helped me prepare. There was also a system at CyberVista for figuring out my strengths and weaknesses – it honed in on the areas I needed to study more."
"Before CyberVista I was given an opportunity to attend a one-week boot camp. Since my employer was paying for it, I did not hesitate to take advantage of the offer. After that one-week boot camp, I came out of there with more questions than I had going in. I did not feel prepared and the training just simply wasn’t enough. CyberVista’s curriculum is an integration of live online lectures, on-demand videos, and an array of self-study tools–it was just what I needed."
"I can’t afford, time-wise, to sit in a classroom for a whole week. Being able to watch the class, and participate, while trying to put my daughter to sleep, was a big boon. Also, the class was organized really well. The multiple online quizzes that we were able to take, and then learn what areas we needed to study more, was really helpful. Also, the light board technology was great. I found it captivating, and it was actually the reason why I signed up in the first place."
"This was my first time studying for a certification through live online training. There were definitely benefits to taking a live online class. For example, you can take your classes from anywhere with an internet connection. I’m happy the training was spread out leveraging multiple learning tools. It was the balance of all of those different aspects that helped to reinforce concepts and instill a strong comprehension of the CISSP."
"I started with a free self-study course and quickly found the accountability was missing. CyberVista’s live interactive course using the light board was a first for me and a great experience overall. It kept me accountable and engaged. The real-life experience of the instructors was evident and their ability to articulate concepts was great. The value of interacting with other students in this live environment was also a significant benefit. It’s not easy getting folks to participate, but CyberVista made it happen."
"After taking the course back in December, this course gave me the discipline to easily digest all the materials that helped me pass the CISSP. The exam was extremely difficult however, I felt more prepared as this course gives you a strong foundation to tackle most of the concepts. I would strongly recommend taking this course for preparation and success for the CISSP!"
"CyberVista stood by me from beginning to end and made time to provide additional test day strategies that helped me successfully pass the CISSP exam. This is a much better alternative to typical boot camps that try to condense too much material in a short period. I plan to recommend CV to colleagues seeking to obtain the CISSP and other industry certifications."