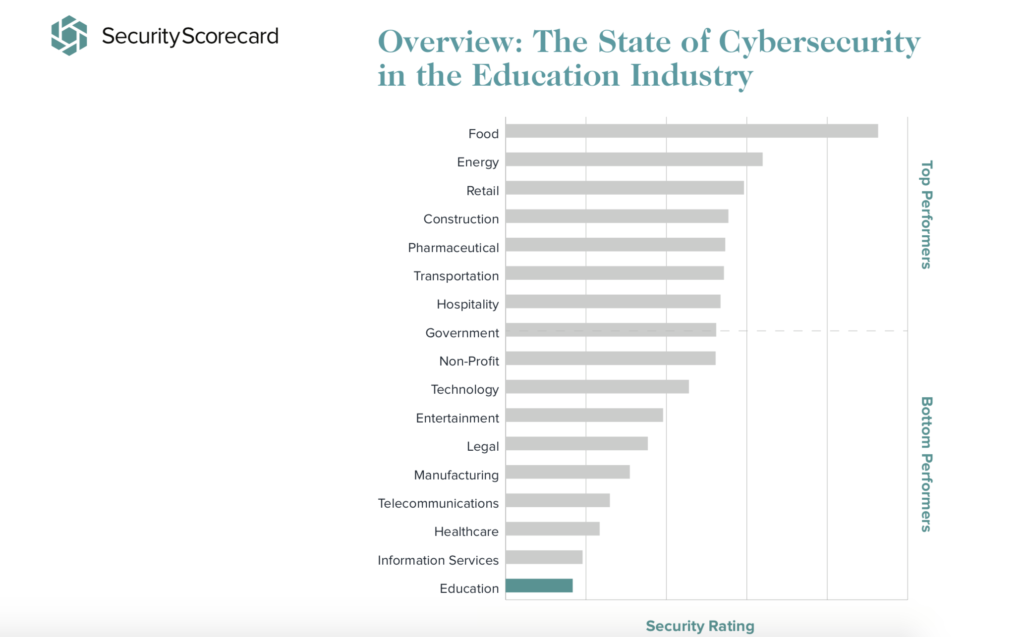
The Education Industry Ranks Worst in Cybersecurity
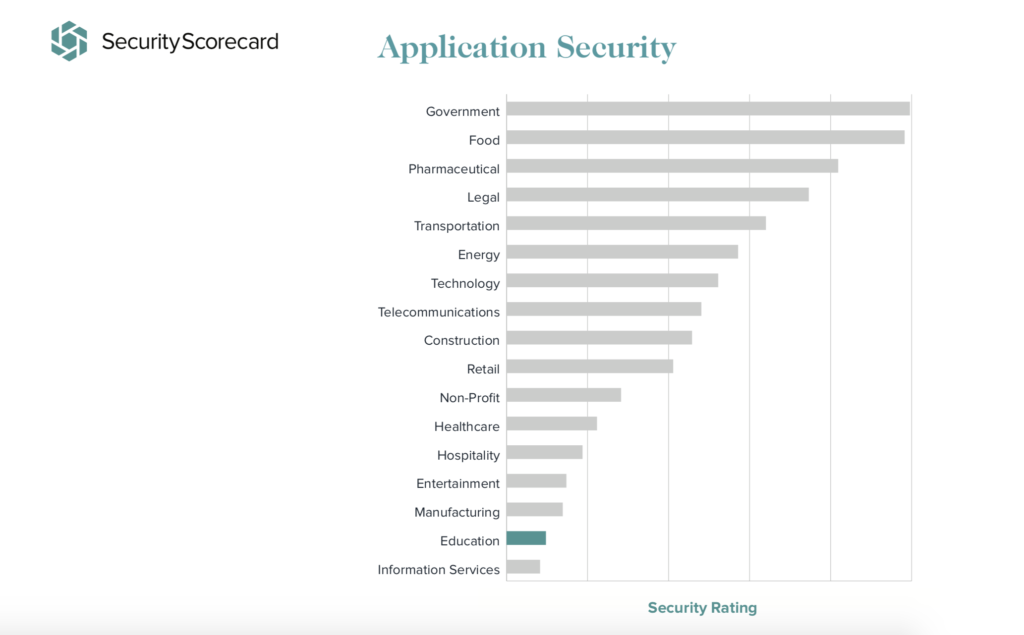
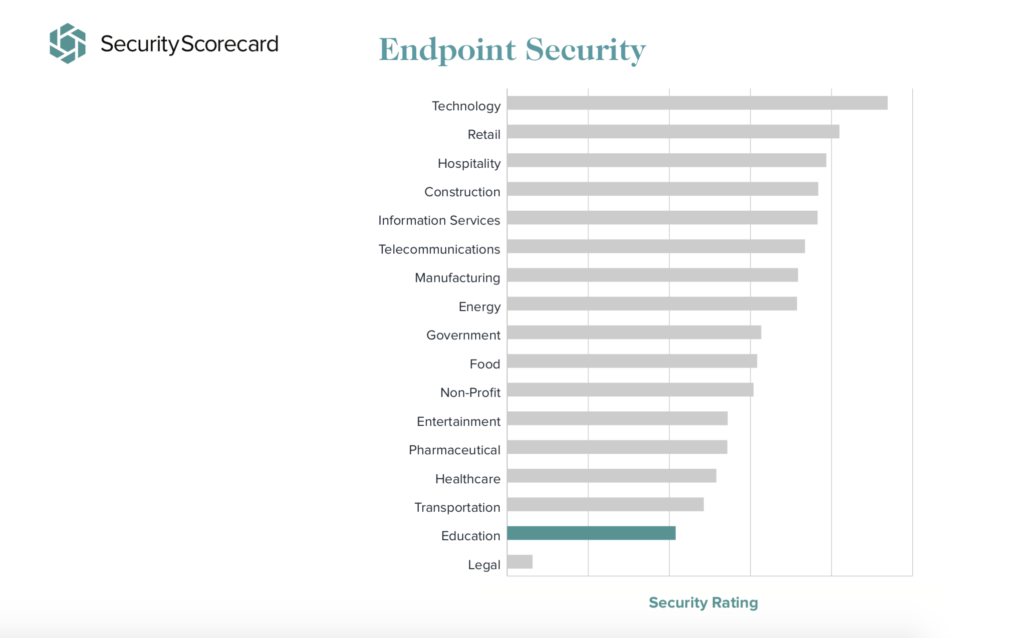
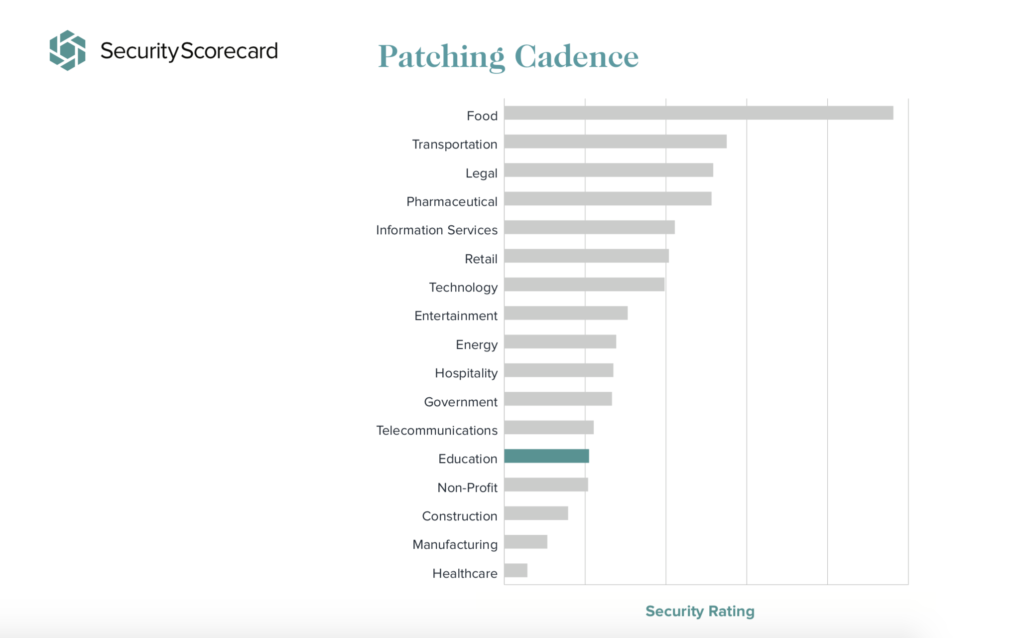
In its 2018 report, Security Scorecard, a company that ranks and rates security on IT infrastructure and risks, analyzed roughly 2400 organizations within 17 industries. The education industry came in last at #17. Education performed particularly poorly in application security, endpoint security, and patching. So why is higher ed in a tough spot when it comes to these areas?
First of all, academic institutions are highly decentralized and have very open environments by design in order to serve educational and research needs in a collegial environment. This, by definition, conflicts with a positive security posture. And like many information security teams higher ed is understaffed, leaving little to no room to properly implement security controls that work let alone have the required staff to monitor and update its network.
All this said, does it even matter that education as an industry is rated worst? It does, and here’s why:
Sensitive Data
Schools collect lots of sensitive information and not in a way your typically business does it. In addition to collecting data from other organizations they work with, universities house a treasure trove of information on each and every one of their students and alumni. The sensitive data includes health data, financial data, as well as a detailed view on the day to day schedules and transcripts of students. Imagine what a hacker could do with such a detailed view of a student’s life? This is prime information for malicious actors to conduct reconnaissance and build expansive overviews of people to be used in phishing or social engineering attacks, giving them a path to access university systems and its network. And once a bad guy gains initial access to a university system then she can wreak havoc in unimaginable ways.
IOT Connections
Beyond the sensitive data they collect, university campuses are connected locally, often nationally, and sometimes even globally to enhance learning, the sense of community, and convenience. There are thousands of devices connected to and through university systems. Edscoop looked into this and spoke with Sam Kassoumeh, chief operating officer and co-founder of SecurityScorecard. He spoke about how students often use more than one device on campus and in-class — computers, phones, tablets or other “internet of things” devices — that while beneficial, Kassoumeh said, create “a heterogeneous environment, where all of the devices are not secured equally.”
IT Staff and Infrastructure
IT staffs are all too often understaffed; and understaffed means that basic security hygiene principles like patching and security audits can go by the wayside. Further, vast and distributed nature of university technology infrastructure coupled with the complexity and sheer number of cyberattacks simply make small staffs incapable of truly protecting networks or even able to prioritize the needs. The 2018 Verizon Data Breach Investigations Report catalogued more than 100 cyber incidents and nearly 300 breaches in the education sector alone. That’s up over the last two years and the problems are only getting worse without the right attention from leadership or its willingness to commit people and financial resources to address these issues.
Options, please?
The education sector, more than any other, has some creative options to help move it from worst ranked in security to first.
Train the Staff
Campuses and universities already talk the talk when it comes to how education is a potentially life-changing (or at least career-advancing) proposition. They should walk the walk by investing in training for their IT and security staffs. From certifications test preparation to skill-specific training to other professional development opportunities. A university cyber team should have every available training opportunity in order to make them more effective in their job responsibilities.
Build and Run a SOC
Universities are also potential hotbeds for building the ultimate cybersecurity workforce. Interestingly, in 2018 five universities banded together and created OmniSOC, a cyber security operations center that provides real-time intelligence sharing and threat analysis for its members. The center operates out of Indiana University and is joined and supported by Northwestern University, Purdue University, Rutgers University and the University of Nebraska-Lincoln.
The center works closely with the Research and Education Networking Information Sharing and Analysis Center (REN-ISAC). The REN-ISAC’S mission is to aid and promote cybersecurity operational protection and response within the research and higher education (R&E) communities.
Want to take it a step further? Universities can provide their students true job-ready operational experience while simultaneously increasing their own security by investing in a student-run and faculty-managed security operations center. What better way to grow a team, give students actual hands-on keyboard experience, and introduce a larger audience to cybersecurity as a profession!
Anything else?
Last place in the rankings is no place for the next generation’s data, so what should the immediate next steps be for the higher education industry? Certainly, awareness of the problem from the very top leadership comes first to help change the culture of cybersecurity at their campuses. A good start for the powers that be on campus is CyberVista’s Board and Executive Cyber Risk Program. As leadership understands cyber risk as an enterprise risk then resources and focus need to follow. Just as cybersecurity has reached among the top priorities for boards of directors in 2019, University presidents and their boards will also see cybersecurity move to be among the most pressing items.
What can students do? Practice cyber hygiene. Say no to phishing. Use strong passwords. And by all means, support each other by closing open browsers on public computers.

