This Week in Cyber
Cybersecurity is a nascent field, but it still has a few significant anniversaries. Welcome to the latest installment of “This Week in Cyber” where we look back on major events that have impacted information technology and cybersecurity. This is more than just an historical exercise. Looking back at historical events can help us understand where cyber has been, where it is headed, and how we should choose to make cyber-risk management decisions in the future.
With February quickly wrapping up, let’s take a look at some of this past week’s significant anniversaries.
February 1 – 26, 1998: Solar Sunrise
The February of 1998 was a month of confusion and panic for the Department of Defense (DoD) and its law enforcement partners. A series of cyber attacks – at least 11 in total – compromised a number of unclassified networks administered by the Air Force, Navy, and Marine Corps. Using a well-known vulnerability in the Solaris operating system, the hackers implanted a surveillance program and collected sensitive government information. The attackers hid their identities by spoofing their geolocation data, making the attack appear to originate in France, Taiwan, Israel, and even the Harvard University computer system. Analysts wondered whether the attack was the work of a foreign adversary; according to the Air Force Information Warfare Center, analysts were “seeing things [they] hadn’t seen before.”
As it turns out, the work of three 16-year-olds was what threw the entire U.S. security apparatus into chaos. In response, President Bill Clinton launched a Cybersecurity plan, beginning efforts to increase coordination between U.S. defense and law enforcement agencies and private companies.
February 15, 1946: First Electronic Computer Invented
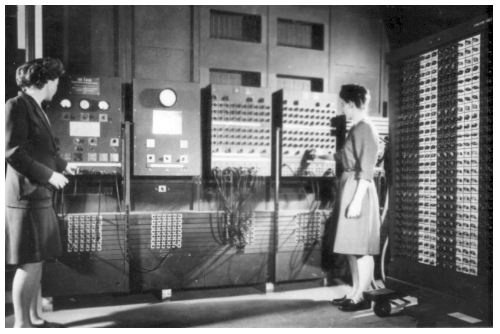
When the University of Pennsylvania fired up its Electronic Numerical Integrator and Computer (ENIAC) in 1946, the institution demonstrated the computational power of computers to governments, industrialists, and the public for the first time. Called the “Great Brain” by the press, the ENIAC could solve math problems – which previously took 30-man hours to complete – in an instant. The computer was a collaboration between the U.S. military and the University. The secrecy surrounding the project led to a rumor that the lights in Philadelphia dimmed whenever researchers turned the computer on.
The principle programmers behind the ENIAC were six women. For years, it was assumed that the most valuable and innovative aspects of the computer was its hardware, not its complex programming. Years later, when the University of Pennsylvania celebrated the ENIAC’s 50th anniversary, the programmers weren’t invited to the event. Even though the machine couldn’t function without their source code, the “ENIAC Girls” and their contributions to the project were not well documented or recognized in their lifetimes.
February 19, 1971: The First Search Warrant for Computer Data
A computer in San Jose, California was the first to be searched by law enforcement after a judge issued a warrant. The search led to conviction for theft of trade secrets.
At the time, the debate over privacy online was still in its infancy, and many technologists and privacy advocates viewed the precedent set by this first search warrant as cause for alarm. The decision led to the proliferation of encryption technology among private citizens, which fueled subsequent legal battles and lasting conflict between Silicon Valley and Washington D.C. for decades.
February 21, 1858: First Burglar Alarm Installed
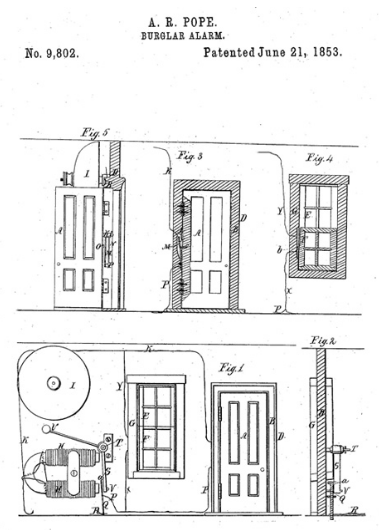
While Boston businessman Edwin Holmes installed and popularized the first alarm, the first electromagnetic alarm system was designed a few years earlier by Boston inventor Augustus Russell Pope. Pope’s intrusion detection gadget was battery-powered and placed on a door or window. An opening in the door or window would trip a spring and send an electric current to a hammer that struck a bell.
Pope became ill shortly after patenting his device and sold it to Holmes. Holmes later took the invention and his business to New York, which, in his words, was where “all the country’s burglars made their home.”
This invention and its impact on physical security remains relevant to this day. In fact, leading security certifications including the CISSP, CEH, and Security+, all devote significant content to physical security and updated intrusion detection systems. Pope would certainly do well in subdomain 3.K of the CISSP exam.
Every practitioner knows that the future of innovation in security and technology is built on both breakthroughs and break-ins from the past. As these snapshots demonstrate, events in history can have monumental impacts on the world we live in today and the world to come.

