What happened at the Ivy Tech IT Challenge I was privileged to attend the Ivy Tech Statewide IT Challenge in…
read moreA Better Approach to Cyber Training Gamification. Innovation. Lab-based. AI driven. Bootcamps. Cyber training companies love to tout these buzzwords…
read moreWomen In Cybersecurity Opening Doors By Shahara Ruth There is an old saying that when one door closes another one…
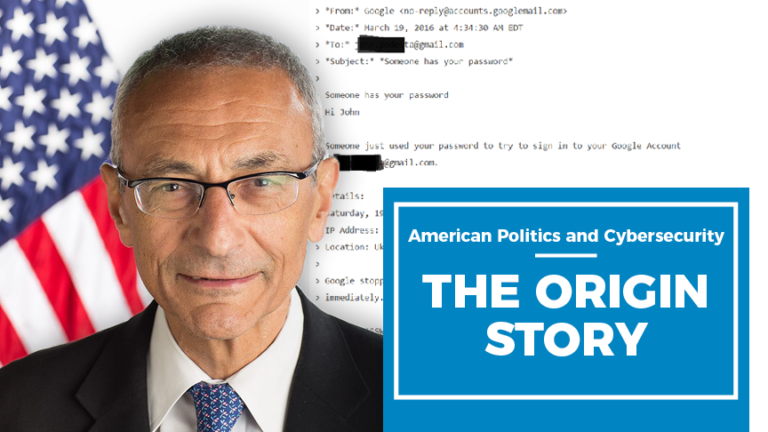
read moreAmerican Politics and Cybersecurity: The Origin Story When Senator Kamala Harris announced her 2020 Presidential bid, she took aim at…
read moreStudent Spotlight: Joe Campbell Information Security Analyst, Verizon Welcome to CyberVista’s Student Spotlight Series. We regularly keep in touch with…
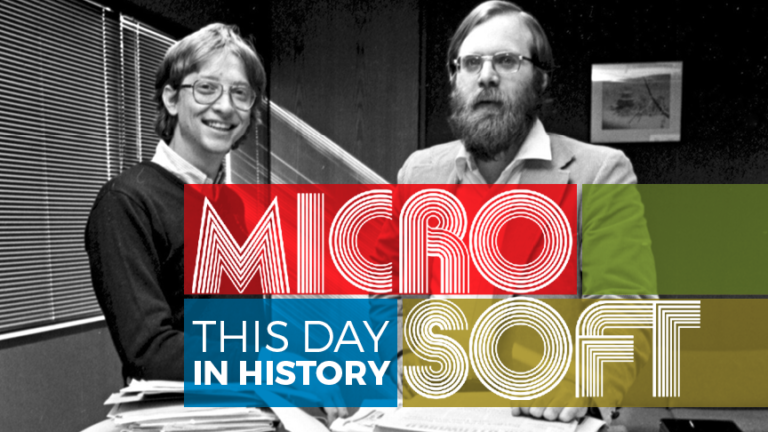
read moreThis Day in Cyber History: Microsoft We’re taking our series, This Week in Cyber History, a bit further with an…
read morePatching. Patching. And More Patching. Does it feel like you (or your company) are always applying patches? Do the security…
read moreStudent Spotlight: Madison Albrecht Senior Consultant at Booz Allen Hamilton Welcome to CyberVista’s Student Spotlight Series. We regularly keep in…
read moreCandidates interested in careers as information security professionals need to know what to expect if they choose to become a…
read moreYou wouldn’t go to a heart surgeon who had gone straight from their pre-med program in undergrad and went on…
read more